[ad_1]
Hackers have been targeting online gaming and gambling companies with what appears to be a previously unseen backdoor that researchers have named IceBreaker.
The compromise method relies on tricking customer service agents into opening malicious screenshots the threat actor sends under the guise of a user facing a problem.
Such attacks have been happening since at least September 2022. The group behind them remains unknown, with indistinct clues pointing to their origin.
Researchers at incident response firm Security Joes believe that the IceBreaker backdoor is a the work of a new advanced threat actor that uses “a very specific social engineering technique,” which could lead to a more clear picture of who they are.
After analyzing the data from an incident in September, Security Joes was able to respond to three other attacks before the hackers could compromise their targets.
The researchers say that the only public evidence of the IceBreaker threat actor they could find was a tweet from MalwareHunterTeam in October.
Tricking customer service
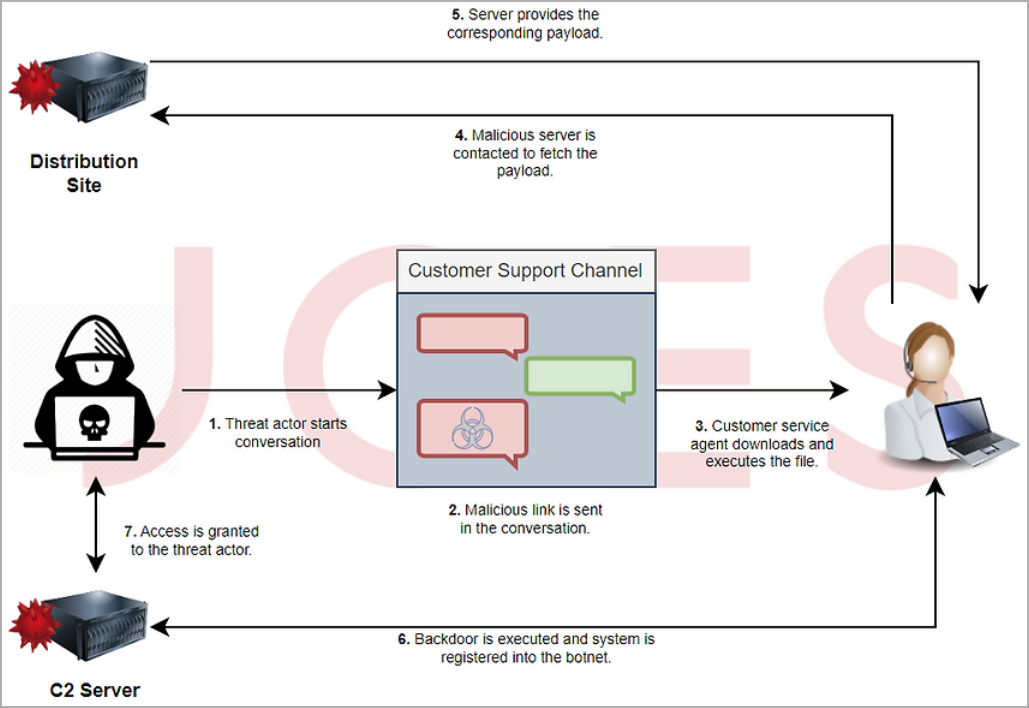
To deliver the backdoor, the threat actor contacts the customer support of the target company pretending to be a user having problems logging in or registering for the online service.
The hackers convince the support agent to download an image that describes the problem better than they can explain. The researchers say that the image is typically hosted on a fake website that impersonates a legitimate service, although they also saw it delivered from a Dropbox storage.
SecurityJoes says the dialogs it examined between the threat actor and the support agents indicate that IceBreaker isn’t native English speakers and purposefully ask to speak with Spanish-speaking agents. However, they were seen speaking other languages too.
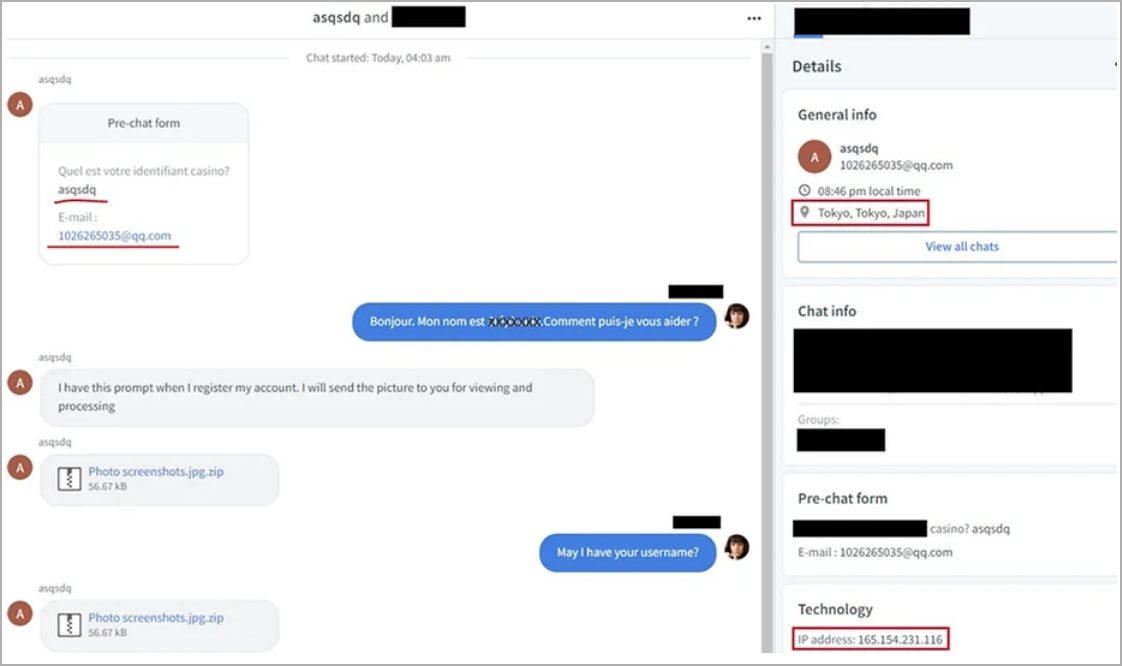
The links delivered this way lead to a ZIP archive containing malicious a LNK file that fetches the IceBreaker backdoor, or a Visual Basic Script that downloads the Houdini RAT that’s been active since at least 2013.
As seen in the image below, the icon for the Windows Shortcut file has been changed to make it look innocuous. The shortcut contains a command to download a MSI payload from the attacker’s server, install it with no user interaction, and run it with no user interface.
Security Joes researchers say that the downloaded malware is “a highly complex compiled JavaScript file” that can discover running processes, steal passwords, cookies, and files, open a proxy tunnel for the attacker, as well as run scripts retrieved from the attackers’ server.
The IceBreaker backdoor
The malicious LNK is the main first-stage payload delivering the IceBreaker malware, while the VBS file is used as a backup, in case the customer support operator is unable to run the shortcut.
The malicious shortcut file poses as JPG image and has its extension modified accordingly. The MSI payload it downloads has a very low detection rate on Virus Total, returning only 4 positives out of 60 scans.
The MSI package features a large set of decoy files to evade signature-based detection tools and analysis engines. The final layer is a CAB archive extracted onto the victim’s temporary folder, dropping the “Port.exe” payload.
Security Joes says this is a C++ 64-bit executable with an unusual overlay, keeping a portion of the data appended to the end of the file. The analysts believe this is a way to hide additional resources from security products.
Upon further analysis, Security Joes figured that the sample is a previously unseen module backdoor written in Node.js, providing threat actors with the following capabilities:
- Customization via plugins that extend the malware’s built-in features.
- Process discovery.
- Steal passwords and cookies from the local storage, particularly Google Chrome.
- Enable a Socks5 reverse proxy server.
- Establish persistence by creating a new LNK file (WINN.lnk) in the Windows startup folder.
- Exfiltrate files to the remote server via web sockets.
- Run custom VBS scripts.
- Take screenshots.
- Generate remote shell sessions.
If the targeted entity has not outsourced customer support services to an external provider, the threat actors can use the backdoor to steal account credentials, move laterally in the network, and extend their intrusion.
At this time, not much is known about the IceBreaker group, but Security Joes decided to publish a report on their findings and share all captured IoCs (indicators of compromise) to help defenders detect and tackle this threat.
The researchers have published a technical report describing the threat actor’s modus operandi and how their backdoor works. YARA rules have also been published to help organizations detect the malware.
Additionally, Security Joes recommends companies suspecting a breach with IceBreaker to look for shortcut files created in the startup folder and check for unauthorized execution of the open-source tool tsocks.exe.
Monitoring the creation of msiexec.exe processes that receive URLs as parameters could also be an indication of compromise just as the execution of VBS scripts and LNK files from the temporary folder.
[ad_2]
Source link